Strategic and Technical Synthesis Document
Introduction: Architecture as Politics
The history of the Internet reads like a progressive sedimentation where the low layers, initially designed for resilience and content indifference, have been covered by application strata of control, centralization, and monetization. In this digital geology, Freenet occupies a singular place. Launched in 2000, the project does not simply constitute a competing application or protocol, but a radical critique, encoded in C++ then in Java, of the trajectory taken by the World Wide Web.
Freenet postulates that freedom of expression is an emergent property of network architecture, not a legal concession granted by states or operators. By proposing a distributed, encrypted, and totally decentralized storage model, Freenet materializes a cypherpunk utopia: that of an acephalous, elusive, and perpetual informational space. This document analyzes this technology under a triple prism: technical, historical, and philosophical. The goal is to understand how this network, although marginalized by usage, remains the most accomplished theoretical model of an "absolute Internet," and how its hollow existence reveals the structural pathologies – surveillance, censorship, industrial centralization – of contemporary Internet.
Genesis and Positioning: The Break with the Client-Server Model
The emergence of Freenet falls within a pivotal period. At the end of the 1990s, commercial Internet consolidated around the client-server model and the DNS (Domain Name System). While this model enabled the Web's explosion thanks to its simplicity of addressing and management, it introduced two Single Points of Failure (SPoF) that later became major political control levers: the IP address, which physically locates the machine, and DNS resolution, which subjects content access to a central authority capable of revoking a domain.
It is in this context that Ian Clarke published in 1999 his thesis entitled A Distributed Decentralised Information Storage and Retrieval System. The Freenet project was born from this academic work with an explicit intention: to make censorship technically impossible. Unlike Napster, which aimed at file sharing with a centralized index, or Gnutella, confronted with scaling problems due to query flooding, Freenet was designed with an absolute priority: anonymity. The founding axiom is that freedom of expression requires total anonymity of information producers and consumers. To achieve this, the network introduces the concept of blind storage: nodes store encrypted data fragments without knowing their content, thus offering "plausible deniability" to operators.
Anatomy of a Dissidence Architecture
Freenet's architecture does not merely hide information; it fundamentally rethinks how information is addressed, stored, and retrieved. It abandons the location paradigm (where is the data?) for mathematical identification (what is the data?).
Key-based Routing and the "Small World" Effect Freenet operates as an overlay network above TCP/IP, ignoring the underlying IP topology. It uses a specialized distributed hash table (DHT) where each inserted file is assigned a unique key. Routing relies on an algorithm inspired by Small World Networks. Each node has its own identity and a routing table containing the addresses of its neighbors and the keys they are likely to possess. When a query is issued, the node transmits it to the neighbor whose identifier is mathematically closest to the searched key. The major innovation lies in the network's learning mechanism: when a path is found, intermediate nodes cache the data during its return (Caching) and adjust their routing tables. The network topology thus optimizes itself organically according to demand, creating virtual "highways" for popular content.
Key Typology and Immutability The nature of information is structured by different types of cryptographic keys. The CHK (Content Hash Key), derived from the SHA-256 hash of the content, guarantees absolute integrity: if one bit changes, the key changes. This is the basis of network immutability. The SSK (Signed Subspace Key) allows the creation of personal spaces where only the private key holder can insert content, ensuring author authenticity. This architecture makes dynamic server-side modification as known on Web 2.0 (PHP, dynamic databases) impossible. Freenet is a static datastore; an update is technically a new insertion.
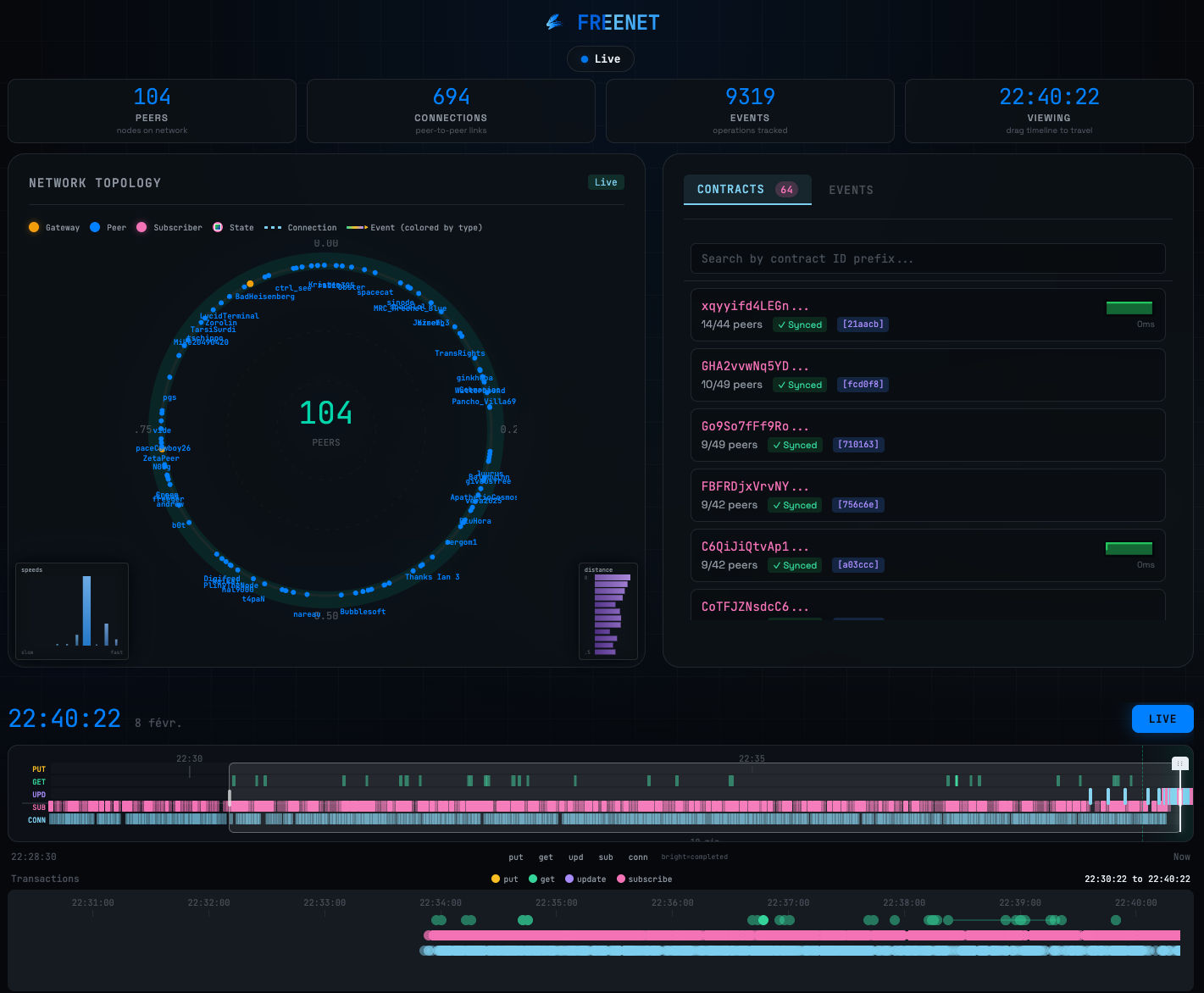
Darwinian Storage and Persistence Devoid of a central server, the network uses the disk space allocated by each user to form a global hard drive. Data persistence follows Darwinian logic. Since space is finite, when a node is saturated, it deletes the least recently requested data (Least Recently Used - LRU). The technical consequence is massive replication of popular content, making it fast to access and uncensorable, while unpopular content tends to disappear if not regularly reinserted. Freenet is not an eternal archive by default, but a collective working memory maintained by attention.
Structural Distinction It is imperative to distinguish Freenet from its counterparts. Where Tor anonymizes TCP transport to access the classic Web (privileging low latency), and where IPFS aims at efficient content-addressed storage without anonymity by default, Freenet acts as an autonomous safe. It combines storage and anonymous routing with high latency, sacrificing interactivity for maximum censorship resistance.
Evolution and Marginalization: The Cost of Freedom
Freenet never exceeded niche network status. This marginalization is not accidental, but the direct consequence of the "Security Trilemma" (Anonymity, Security, Performance). Freenet sacrificed performance on the altar of absolute security. The advent of Web 2.0 sealed its mainstream fate: users massively opted for the convenience, speed, and real-time interactivity offered by centralized platforms, tacitly accepting surveillance in return. Freenet's user experience – slowness, static content, technical friction – is antithetical to the modern attention economy.
Moreover, the total absence of moderation and perfect anonymity inevitably attracted reprehensible content. Although the community defended the tool's philosophical neutrality, this reality hindered adoption by "mainstream" political activists and journalists, often more inclined to use Tor. Facing threats of active detection by states like China, Freenet had to evolve toward a pure "Darknet" architecture (Friend-to-Friend), where a node only connects to trusted peers. While this theoretically makes the network impenetrable to Sybil attacks, it fragments the social graph and drastically limits content discovery.
Geopolitical Parable: Centralized Internet and Lost Sovereignty
Freenet's analysis acts as a revealer of conventional Internet pathologies. Its marginal existence highlights by contrast the immense centralization machinery operating today. Today's Internet resembles a technological feudalism where infrastructure (AWS, Google Cloud), protocols (DNS, ICANN), and distribution (CDN like Cloudflare) are concentrated in the hands of a few actors, mostly American. In this scheme, digital sovereignty is an illusion. A legal decision or modification of a platform's terms of use is enough to make a digital entity disappear.
Modern censorship has also mutated. It is no longer just brutal blocking, but proceeds through structural invisibilization: deplatforming, shadowbanning, and algorithmic filtering. Freenet, through its blind routing architecture, makes deplatforming impossible (no server to unplug) and shadowbanning inoperative (routing is mathematical, not social). However, it suffers from "censorship by noise": without efficient centralized search engines, finding relevant information requires high cognitive effort. Moreover, facing astroturfing and opinion manipulation that saturate the clear Web, Freenet opposes a "Slow Web" model where virality is mechanical and not algorithmic, making artificial consensus manufacturing economically costly.
Ethos and Vision: The Internet That Could Have Been
Freenet embodies an alternative teleological vision. If the Web was optimized for commerce and flow, Freenet was designed for asymmetric information warfare and memory. The use of hash keys freezes content in an immutable version, philosophically bringing the project closer to Blockchain: a digital book whose pages cannot be torn out.
By completely decoupling logical address from physical address, the network makes geographical jurisdiction irrelevant. Data is everywhere and nowhere, fragmented and encrypted. It is the technical materialization of cyberspace independence, making copyright application or state censorship technically impossible without destroying the network itself. This radical posture, placing the right to communication above property rights, contributed to its isolation, making it incompatible with cultural industry business models.
The Role of Silent Witness
Analyzing Freenet twenty-five years after its creation does not consist of evaluating a startup that failed to conquer the market, but of observing an architecture that succeeded in its technical mission: creating an uncensorable space. Its relative "failure" in terms of mass adoption is the symptom of a societal choice. Connected humanity, confronted with the alternative between absolute freedom (with its costs in performance and responsibility) and surveilled comfort, massively chose comfort.
Freenet remains today a "reserve network," a dormant infrastructure. It does not serve daily use, but constitutes structural life insurance. If filtering, state censorship, or corporate control were to reach a critical threshold making conventional Internet totally impracticable for dissidence, Freenet and its spiritual heirs would offer the necessary tactical retreat. Ultimately, this technology is not a relic of the past, but a permanent warning: it reminds us that Internet centralization is not a technical inevitability, but a political construction, and that another model remains available for those ready to pay its price.